Edit
Big time pocket vulnerabilities
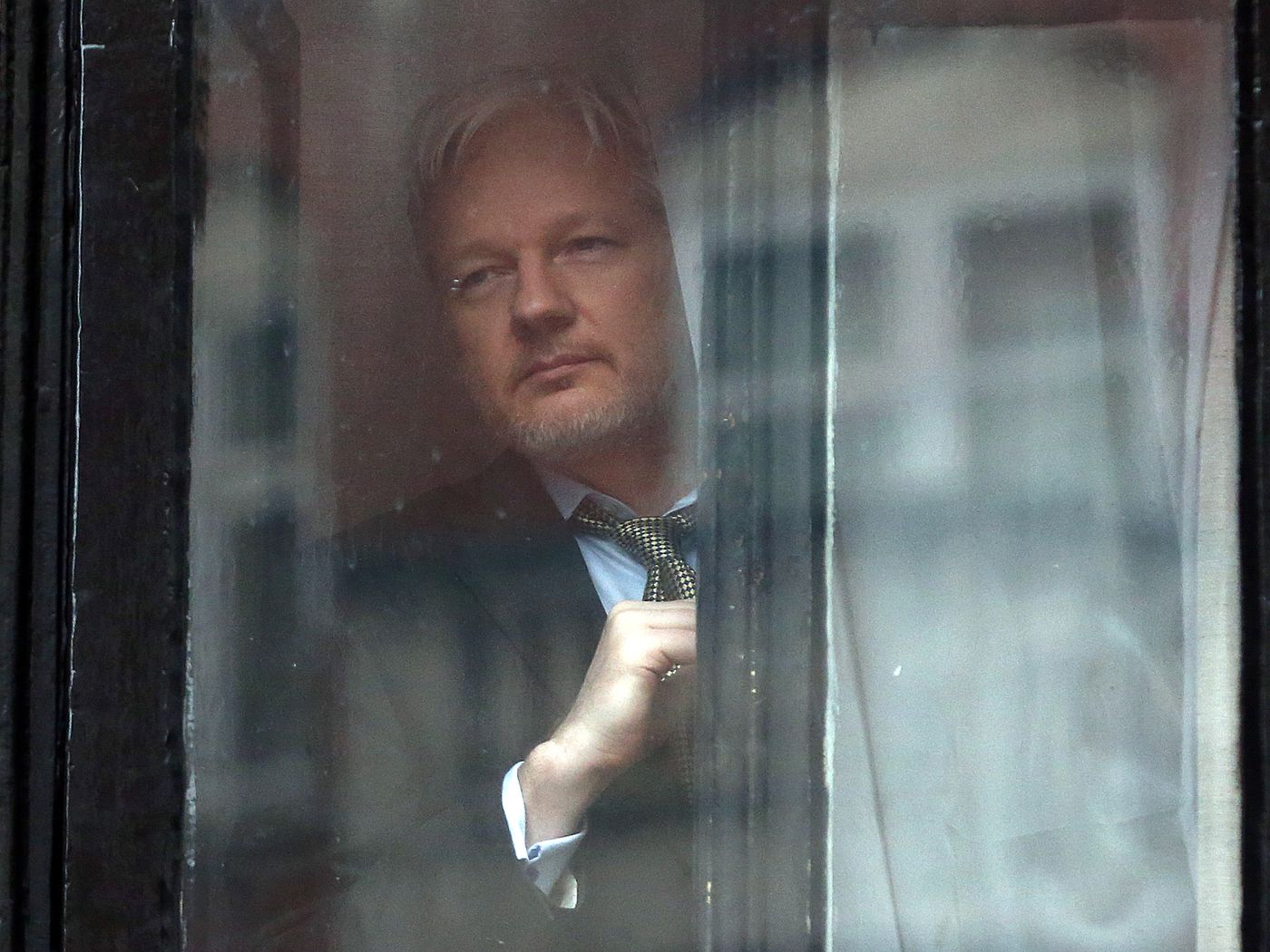
I was asked for a comment on some research into mobile app IT security and identified the Operating System and physical proximity as the two key attack vectors. A couple of days later, Wikileaks released material related to the CIA's aggressive hacking arsenal. Much of it aimed at mobile phones.
- Rene Millman's original article
 50 banking smartphone apps fail on securityAnaysis of mobile applications of 50 of the world’s top 100 banks has found all to be vulnerable to several security threats.
50 banking smartphone apps fail on securityAnaysis of mobile applications of 50 of the world’s top 100 banks has found all to be vulnerable to several security threats.- Some further thoughts by me; I identify the fact that we have built Risk Control portfolios to manage and mitigate some of these vulnerabilities, although the phone needs to be with you to be of use and so physical proximity cannot be denied.
- Recode on the Wikileaks dump, who also seem to be more concerned about laptops and silly names
 Weeping Angel, Brutal Kangaroo and other secret CIA code names from the WikiLeaks surveillance leakOther code names include Fine Dining, Cutthroat and HarpyEagle.
Weeping Angel, Brutal Kangaroo and other secret CIA code names from the WikiLeaks surveillance leakOther code names include Fine Dining, Cutthroat and HarpyEagle.- ORG states that encryption still works, the hacks rely on hacking the device.
 Yes, the CIA can hack phones but Signal and WhatsApp are still safe for nearly everyoneThe CIA can hack phones but Signal and WhatsApp remain very good ways to communicate when using a mobile phone for nearly everyone. The worst thing to do would be to throw our hands up in the air and give up on our digital security.
Yes, the CIA can hack phones but Signal and WhatsApp are still safe for nearly everyoneThe CIA can hack phones but Signal and WhatsApp remain very good ways to communicate when using a mobile phone for nearly everyone. The worst thing to do would be to throw our hands up in the air and give up on our digital security.- Bruce Schneier comments here, on the age of the material and the likely source
 WikiLeaks Releases CIA Hacking Tools - Schneier on SecurityWikiLeaks just released a cache of 8,761 classified CIA documents from 2012 to 2016, including details of its offensive Internet operations.
WikiLeaks Releases CIA Hacking Tools - Schneier on SecurityWikiLeaks just released a cache of 8,761 classified CIA documents from 2012 to 2016, including details of its offensive Internet operations.- It seems that the CIA lost the cyber weapons, which is a bit careless of them but reinforce the argument that Government secrets about people (or in this case software) will leak. Privacy is damaged immediately or via the cyber weapons. It's an example of what will happen if there are government mandated back doors.
 More on the CIA Document Leak - Schneier on SecurityIf I had to guess right now, I'd say the documents came from an outsider and not an insider. My reasoning: One, there is absolutely nothing illegal in the contents of any of this stuff. It's exactly what you'd expect the CIA to be doing in cyberspace.
More on the CIA Document Leak - Schneier on SecurityIf I had to guess right now, I'd say the documents came from an outsider and not an insider. My reasoning: One, there is absolutely nothing illegal in the contents of any of this stuff. It's exactly what you'd expect the CIA to be doing in cyberspace.- ORG's comments on the UK Government's culpability and high lighting the fact that the transatlantic intelligence agencies have discovered software vulnerabilities and failed to inform the product authors.
 CIA and GCHQ hacking – they must clear up their own messUS intelligence agencies are working with the UK to stockpile vulnerabilities that they can use to hack Windows and Mac computers, iOS and Android smartphones, and smart TVs. The UK Government has serious questions to answer.
CIA and GCHQ hacking – they must clear up their own messUS intelligence agencies are working with the UK to stockpile vulnerabilities that they can use to hack Windows and Mac computers, iOS and Android smartphones, and smart TVs. The UK Government has serious questions to answer.
