Yesterday, attended a session convened by the BCS North London branch, called “Data Privacy – How Private is IT?” The presentation was given by two PWC staff members in two parts, the first was a forward looking review at the proposed EU Data Protection Regulation by Kyrisia Sturgeon and the second part a scenario based exploration of good data protection practice led by Pragasen Morgan. To me the coming key changes in the law are that all companies will need to have a qualified data protection officer, and it implements a right to be forgotten, or more accurately a right to be unindexed.
In the first part of the presentation, Kyrisia Sturgeon walked through the expected changes in the EU Regulation. The Parliament has completed its consideration, which is now being considered by the Council. It was argued that the transition from the current Directive, which requires national implementation and interpretation to a Regulation which is law is to bring about standardisation and to reinforce the single market. It was argued that the law will promulgate the following changes,
- There are redefinitions in scope, there is a new role, that of producers which is aimed at enclosing the system producers, a necessary step as storage i.e. data moves to the cloud. In addition the law is to be extra-territorial, the trigger for “standing” is to be the citizenship of the data subject. (We already have the roles of subject, controller and processor).
- There is a new requirement to have a Data Protection Officer, who will need to be an expert and currently will have a four year tenure and need to be a board member. (It’ll be interesting to see how that works out since board roles and powers differ between member states and these words will make out sourcing hard.)
- Data Protection needs to be designed in by default. There will need to be evidence of compliance which means that software developers will need to perform privacy impact assessments as part of the change approval process and this will also have significant impact on the “System Producers”.
- There is to be a tightening up of the consent rules, which will need to be explicit, permit withdrawal and not be conditional on other agreements. This it would seem is an attempt to reduce bundling of services with privacy consents.
- There are requirements to implement the emerging “right to be forgotten”. For most end user IT concerns, this relates to keeping data only for as long as it is required for the purpose for which consent has been given. The recent case at the CJEU states that Google, and presumably other search providers must not display irrelevant or out-of-date links in the search query responses. (This issue provoked a lot of interest which I reflect on below.)
- The Regulation tries to make enforcement simple and cheap. It’s hard to define the location & hence the jurisdiction of a privacy infringement but the Regulation tries and tries to define a one stop shop for enforcement and remediation.
- There is a requirement in the new law to report breaches within 72 hours. Currently there are countervailing pressures; companies probably don’t want to be exposed by hackers or clients, but also fear the reputation damage that reporting entails. (This duty may be as a result of the Cyber Security Directive.)
- Penalties for corporates for breach of the law are to be increased, to 5% of worldwide turnover (or 100m EUR), this is an increase from the current maximum penalty of 500,000 GBP.
The meeting was particularly interested in the Right to be Forgotten. The CJEU has stated that Google must not report on outdated, irrelevant, inadequate or excessive information, specifically if the search argument is a person’s name (or presumably other personally identifying data). The test case involved a (Spanish) plaintiff asking for a newspaper article reporting on a discharged court case to be removed from Google’s index. The current ruling means that Google must be able to delete or suppress entries from search queries.
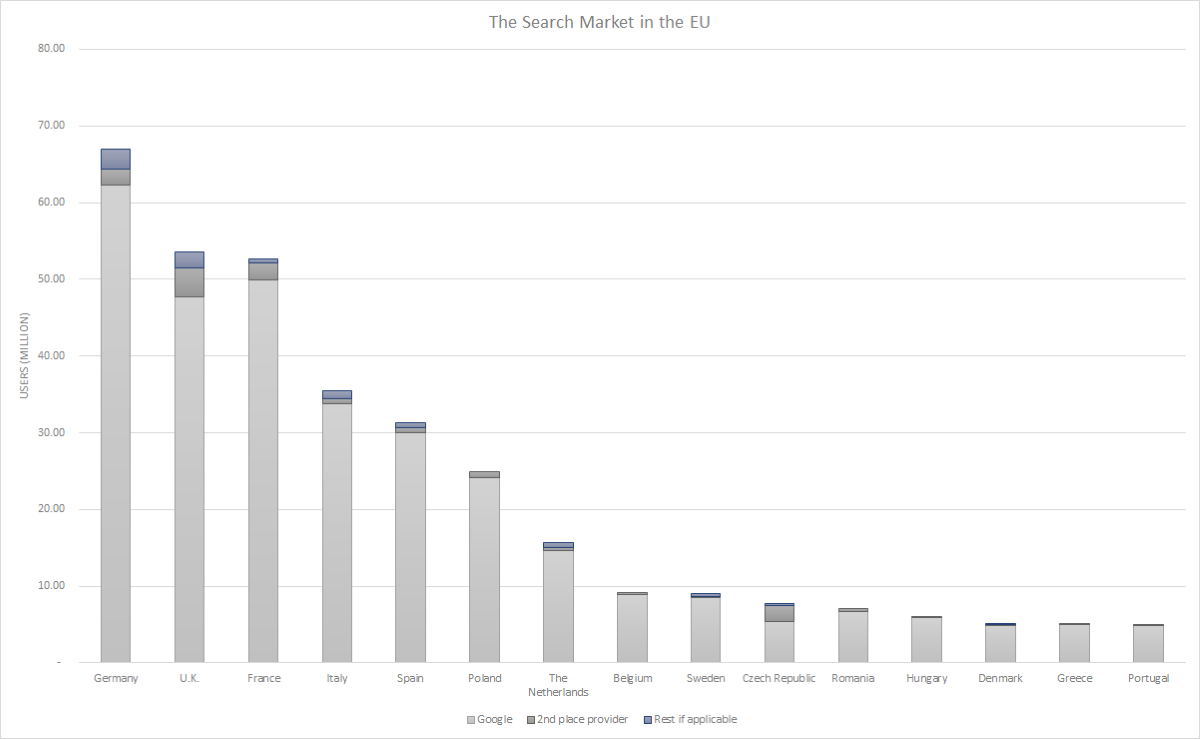
In order to write this blog, I found this blog article at the LSE and this article at insideprivacy.com. (If I have reflected the Law correctly, this suggests that Google’s approach of blacklisting pages on request is excessive.) I am assuming that legal behaviour would be mandated on other search engine providers but Google’s European market share is enormous. As a result of this meeting I decided to see what Google’s market share was; it led me to make this page, “Google’s Market Share” on my wiki. Only in the UK & Czech republic is Google’s share under 90% with on the whole Microsoft’s Bing being the second place provider. There’s no question that it has an effective monopoly.
This level of market share does not exist in the USA, which maybe one reason why there’s some ‘patriotic’ political resistance to their regulation by the EU. For the caveats on the numbers & chart, read the wiki article.
The weight of opinion in the room felt that the CJEU ruling was an over reach; it’s only when you realise that a key part of the judgement is that it’s the query search that breaches privacy, not the retrieval. Otherwise how can it be sensible to restrict Google’s actions while not taking down the linked article/content? This question is answered in the LSE blog, and Google’s 98% market share of European search reinforces these arguments.
A further problem for many of those present is how as multi-national companies, particularly the European offices of US companies, could they ensure their software solutions, particularly if they are ‘soviet-style’ client server solutions meet the needs of new European data protection laws. It is my experience that US companies are well aware of the need to meet both local law and the law of the jurisdiction of incorporation. I have written about these issues on linkedin (here & here) and also on my blog (here).
The desire to create a onestop shop is going to be difficult. At the moment, it looks like the jurisdiction of incorporation of the controller, processor or producer will determine the regulatory jurisdiction, but this will be complicated depending on who and how many are complaining and where they’re located. There are planned to be triggers for other regulators to declare an interest. The complexity is explained at this Out-Law.com article. It is clearly a sticking point at the Council of Ministers and the British Government is likely to hold out for minimal supra-national jurisdiction i.e. the Government doesn’t want foreign courts deciding on British law. Legal resolution is becoming the bug bear of EU law, most especially when dealing with the digital economy; the internet is challenging the nation state’s jurisdictional monopoly because determining the location of an event is becoming harder and harder.
The need for evidence for Privacy by Design will almost certainly create changes in the design and change/release management processes. There is likely to be a need for privacy impact analysis as part of the change impact analysis, although the extent to which this differs from current risk assessments given that privacy is one dimension of the IT security problem is moot. It’ll be interesting to see if the growing need will change standard Security Architecture patterns and the component/role allocation between the application and the operating system. It seems to me that there is going to need to be a new generation of entitlements enforcement solutions. Kerberos and LDAP/AD leave detailed privacy enforcement to the application; companies are going to have to better.
The new requirements for a DPO create business opportunities. At the moment, the majority of Chief Privacy Officers, where they exist are Lawyers, often equipped to help answer the question, what is the least I need to do. Like compliance the ideal CDPO requires a multi-disciplinary approach needing to understand both the technology and the law however, I’d argue the technology is harder, which is why the law is often hard to understand or comply with. An example being how to implement immutable records for Dodd Frank reporting. The Law states that the records must be unchangeable, how is this implemented in technology, especially as in this example, the records may need to be kept in excess of fifty years. While eventually a court will determine if software protection is good enough, judgements today are being made by technologists & engineers. It is felt that the approach will be risk based, so low risk companies can operate at lower levels of competence. In order to sensibly execute a DP policy, companies will need a comprehensive data model and an information security classification policy and implementation. You need to know what data you hold and what rules you need to apply to it. One wonders if these new roles will create an accreditation scheme. Since there’s money it, someone will try and it seems to me better if the public sector gets there first. In the USA, there is the International Association of Privacy Professionals, although their courses are based on US Law only, and one has to question if Europe really wants the professional standards for Data Privacy to be defined and accredited by a US incorporated entity. (We can be sure that the lawyers will not permit themselves to be accredited by foreign entities, but then they still have a pre-entry closed shop.)
An unanswered question is the extent to which the work can be outsourced or consultants can be relied on, firstly for the role and work of CDPO, but also if increased privacy regulation will change the economics of I.T. outsourcing. In finance, the rules contained in CP 142 apply, in that regulatory liabilities cannot be insured or passed off through professional services contracts. The regulatory liability and fines remain that of the principals. This will create a significant due diligence effort where data controllers are looking to outsource their IT to traditional hosting companies or to cloud providers irrespective of whether they are looking to buy SaaS or IaaS. The Cloud Security Alliance is building a common knowledge domain and certification schemes to facilitate this work. I wonder if CP 142 will inhibit the trend by data controllers to write appropriate behaviour into their IT supply contracts as an alternative to the intergovernmental agreements i.e. the
All in all an interesting meeting. A lot is going to change.
ooOOOoo
This article has been backdated to the date of occurrence, like many it took me several months to find the time.
The key reference’s used in the article are repeated below.
- http://blogs.lse.ac.uk/mediapolicyproject/2014/05/13/european-court-rules-against-google-in-favour-of-right-to-be-forgotten/
- http://www.insideprivacy.com/international/european-union/article-29-working-party-agrees-right-to-be-forgotten-guidance-following-may-2014-cjeu-ruling-against-google/
- http://www.out-law.com/en/articles/2014/june/plans-unveiled-to-remodel-proposed-one-stop-shop-regulation-of-data-protection-in-the-eu/
Image Reference : Adam Lang, @flickr 2006 CC BY-NC-SA (6th Jan 2015)